Pricing, features, roadmap, reference customers — enterprise TMS RFPs rehearse these in that order. In real life, every serious evaluation eventually collapses into one question from the Enterprise Architect in the room: "Can you actually talk to our ERP?" If the answer is unconvincing, nothing else on the slide deck matters. This post describes what a convincing answer looks like, told from the side of the team that writes the integration code — not the sales deck that glosses it.
We build NiuX TMS — a transportation management system that ships under three private-deployment license tiers (Enterprise, Flagship, Source Code) and runs inside the customer’s own VPC, private cloud, or on-premises data center. Across that deployment base, we have done dozens of integration projects connecting NiuX TMS to SAP (ECC and S/4HANA), Kingdee (K/3 Cloud, Cloud Cosmic), Yonyou (NC, U8, BIP), and the long tail of industry-specific WMS, billing, and carrier platforms those ERPs stand in front of. The notes below are written out of that experience, not out of a vendor capability-matrix spreadsheet.
”Can you integrate with SAP?” is the wrong question
It is a polite question — which is why it keeps getting asked. But it has no useful answer on its own. A vendor that says “yes, we integrate with SAP” has told you nothing about the actual engineering surface. The useful questions, in order, are:
- Which SAP? ECC on-prem, S/4HANA on-prem, S/4HANA Cloud, SAP Business One, SAP Business ByDesign — these are genuinely different products with different integration protocols.
- Which protocol? IDoc over SFTP, IDoc over MQ, RFC/BAPI, OData services, SAP CPI flows, custom ABAP extensions, plain REST on a Z-table-backed middleware. Each carries different latency, reliability, and security characteristics.
- Which direction? TMS writes to ERP (shipment status, freight invoice posting) vs ERP writes to TMS (sales order, delivery note, master data). Different directions touch different authorization boundaries in SAP, and they matter to your Basis team.
- How often, how much? Real-time single-document push? 15-minute batch? End-of-day file drop? 200k lines per run? All three patterns coexist in the same customer.
- Who owns the mapping? The TMS vendor, a third-party integration consultancy, your in-house SAP team, or “nobody until something breaks at month-end”?
- What happens when it fails? Retry policy, dead-letter queue, reconciliation interface, operational alerting — who pages whom at 02:00 on a Saturday?
Any vendor that cannot answer those six questions against your specific landscape hasn’t integrated with SAP. They’ve answered a checkbox. Integration is specified, not claimed.
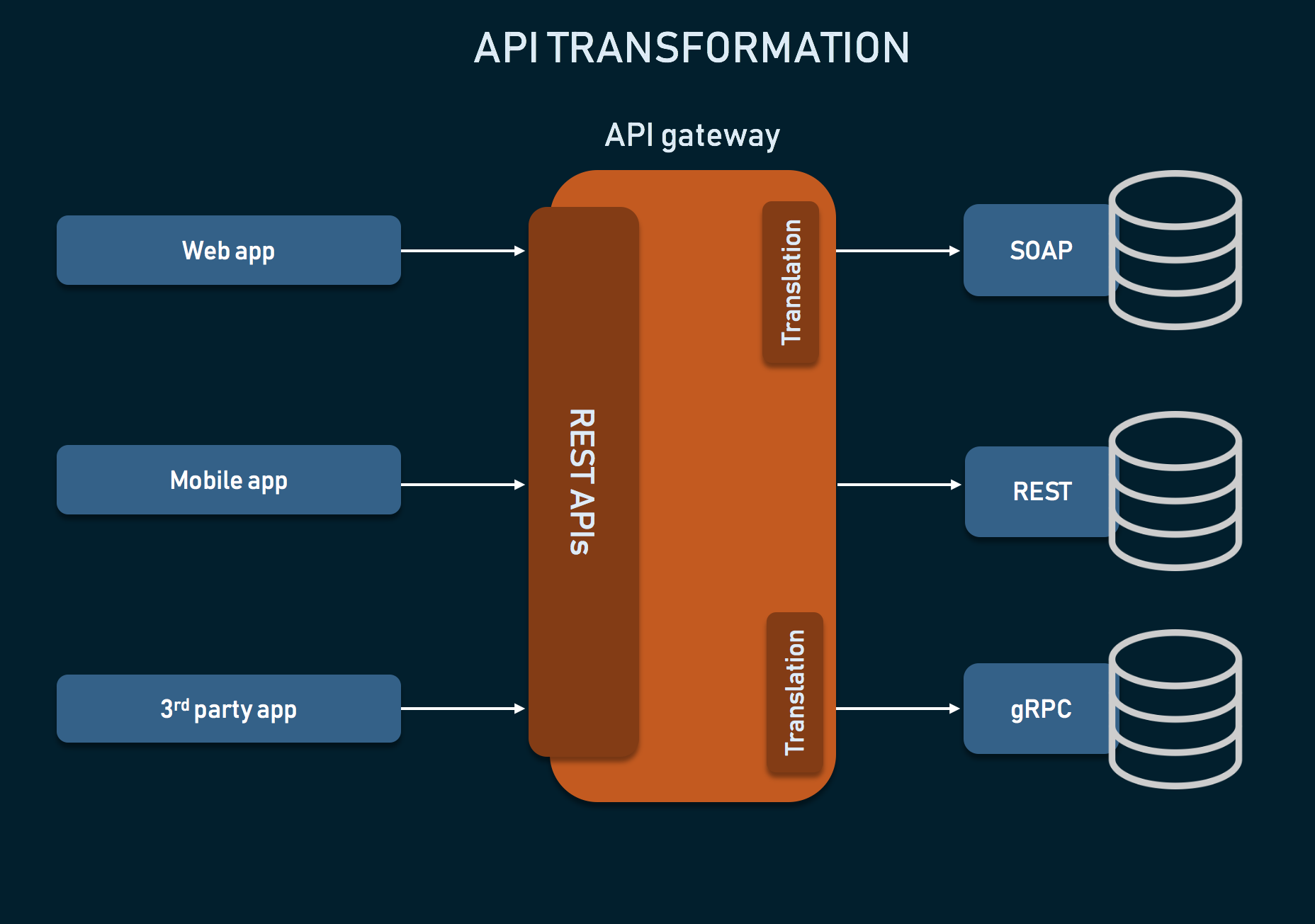
The three integration topologies we actually ship
In production, we end up deploying one of three topologies — or a blend — on every project. Fashion changes; the topologies don’t.
1. File-based exchange over SFTP or enterprise MQ
Still the dominant production pattern in 2026 for SAP-centric enterprises, especially in industries where SAP is also the financial system of record. IDoc XML, CSV, fixed-width positional, occasionally EDIFACT. Dropped into a shared SFTP directory or published onto an enterprise MQ (IBM MQ, RabbitMQ, ActiveMQ).
Why enterprises still prefer this in 2026:
- The security team does not want another inbound API in front of production SAP. File drops live on an already-audited channel.
- Reconciliation is easy: a file either arrived or it didn’t. There is a record on disk.
- Replay is easy: re-drop the file.
- No tight coupling: if TMS is down for 30 minutes, SAP doesn’t notice.
Where we ship it: nightly master data sync (materials, customers, vendors, plants), daily sales-order import, end-of-day waybill settlement posting to FI, monthly reconciliation extracts. On the steel and paper projects where we’re handling hundreds of thousands of document lines a day, file-based still wins on cost and reliability.
2. Synchronous API with authenticated service accounts — inside the VPC
For real-time paths where a 15-minute batch is not acceptable: live shipment status push, dispatch rate shopping, track-and-trace propagation, emergency order re-routing. Here we move to request/response against SAP OData services, SAP RFC via JCo, Kingdee Cloud Cosmic Open API, Yonyou BIP Open Platform, or a Z-endpoint the customer’s ABAP team exposes.
The important detail: because NiuX TMS is deployed inside the same VPC as the ERP, the API call is internal network traffic. That changes everything:
- No OAuth2 token dance across the public internet. mTLS between two internal hostnames. The token lives in a service account in your internal IdP (Active Directory, LDAP, Keycloak), not in a SaaS vendor’s control plane.
- No egress auditing headache. Your InfoSec team doesn’t have to classify the traffic as “data leaving the enterprise.”
- No NAT traversal, no VPN flap as a failure mode. Either the network is up or everything is down.
- Latency budgets are measured in milliseconds, not tens of milliseconds plus WAN variance.
Where we ship it: live status bus between TMS waybill state machine and SAP delivery status fields, synchronous rate lookup against a carrier-contract master in SAP, master data “pull on demand” for long-tail references.
3. Event bus for multi-subsidiary groups
For groups with a shared-service ERP landscape and many subsidiaries — think a Fortune 500 with 20–270 operating entities sharing one SAP instance, or a Manufacturing 500 group with a mixed SAP/Kingdee/Yonyou footprint — the clean shape is a message bus (Kafka, RabbitMQ, Rocketmq, or an in-house enterprise service bus).
TMS publishes business events: Waybill.Dispatched, Waybill.Delivered, Settlement.Confirmed, Invoice.Posted. Each subsidiary’s ERP consumes the events it cares about, on the schema contract the subsidiary has agreed to — not on whatever schema the shared SAP instance happens to expose this quarter.
This topology is what we shipped for the Anhui Construction digital freight backbone and for the century-old building materials group running 270 subsidiaries. Without a bus, every one of those 270 subsidiaries would need its own point-to-point mapping, and every SAP landscape change would cascade into a coordination problem across all 270.
On a project, we rarely pick exactly one topology. A typical Flagship-License customer ends up with nightly SFTP for master data, a real-time API for dispatch-critical paths, and a bus for multi-subsidiary event distribution — all of it deployed inside their VPC and all of it audited to their InfoSec standard.
What “a SAP connection” actually contains
To put a number on it: a mid-to-large Flagship-License deployment typically has 8–12 bidirectional integration endpoints with SAP alone, before we even start on WMS, carrier portals, and billing. For each endpoint, the discovery artifact we build in the first two weeks of the project lists:
- Endpoint name — e.g. "Sales order import from SAP SD"
- Direction — SAP → TMS or TMS → SAP (or both)
- Protocol — IDoc/SFTP, OData, RFC, CPI, custom REST
- Frequency — event-driven, 5-minute batch, 15-minute batch, hourly, end-of-day
- Trigger — who initiates the transfer, and how replay is handled if it fails
- Owner — the exact person or team responsible for keeping the mapping correct, with fallback
- Reconciliation path — how we know that what we sent equals what was received
Concretely, an ECC-era SAP deployment typically carries: DELFOR for delivery forecasts, DESADV for advance ship notice, INVOIC for billing posting, CREMAS for vendor master, DEBMAS for customer master, MATMAS for material master, SHPMNT for shipment documents. An S/4HANA deployment trades some of these for OData services (sales order, outbound delivery, billing document) plus CPI flows for cross-system orchestration. Kingdee Cloud Cosmic and Yonyou BIP both publish their own “open platform” APIs which are modern REST with JSON and — in our experience — surprisingly well-documented; the delivery challenge there is authorization scopes, not protocol.
No TMS vendor can ship all of this prewired. What they can ship is: a connector library that covers the 80% case, a documented mapping framework that absorbs the remaining 20%, and an integration team that knows the difference between a DELFOR and a DESADV without having to Google it.
Why private deployment makes integration cleaner, not harder
The common assumption — “SaaS is easier to integrate because it’s already on the cloud” — does not survive contact with a real enterprise InfoSec review. In a private-deployment model, the TMS and the ERP live inside the same network boundary, and that has second-order consequences that SaaS TMS vendors quietly hope you don’t think through:
- Compliance posture. GDPR, PDPA, PIPL, Saudi NDMO, Brazilian LGPD — all evaluate “traffic between TMS and ERP” as internal traffic when both systems live in your VPC. No cross-border transfer paperwork. No Standard Contractual Clauses. No sub-processor disclosure. In regulated industries — pharma, bonded logistics, government-linked shipping, defense-adjacent manufacturing — this is often the entire reason the deal is on the table.
- Authentication model. Your existing Active Directory or LDAP is the authority. Service accounts for TMS ↔ ERP calls are standard internal identity objects, not a second identity plane maintained by a SaaS vendor.
- Audit trail. Your SIEM already ingests traffic between TMS and ERP. You don’t have to layer a second audit trail from the SaaS vendor’s control plane and then argue with internal audit about which one is authoritative at year-end.
- Failure blast radius. Your ERP’s availability no longer depends on the SaaS TMS vendor’s cloud region, their upstream CDN, your egress path across the public internet, or their renewal calendar.
- Change cadence. TMS-side changes to integration mappings are deployed on your release train, not theirs. The rule-engine / form-engine / process-engine authoring rights that come with the Flagship License specifically exist so that most integration-adjacent changes (new field, new rule, new routing trigger) are configuration on your release schedule, not a ticket in a SaaS vendor’s backlog.
In 2026, a non-trivial share of our top-tier deals are driven primarily by the sentence “we need the TMS in the same network segment as our SAP.” The procurement gate is rarely total cost of ownership. It is almost always who controls the network edge between the two systems.
Kingdee and Yonyou — why they matter for Asian industrial groups
Anyone selling enterprise TMS into APAC who assumes “SAP is everywhere, Kingdee/Yonyou are second-tier” is underwriting a market-entry mistake. The accurate picture is:
- Group HQ often runs SAP, but many subsidiaries — especially those acquired or grown organically in Mainland China, Hong Kong, Taiwan, and SEA — run Kingdee K/3 Cloud, Kingdee Cloud Cosmic, Yonyou NC, Yonyou U8, or Yonyou BIP. Depending on the industry, the ratio inside a single group can easily be 30–50% non-SAP.
- These are not lightweight products. Kingdee and Yonyou each have decades of enterprise deployment, deep industry packs (manufacturing, retail, pharma, construction), and in some regional customizations are objectively better documented than SAP’s equivalent extension.
- Procurement implication: if the TMS vendor can’t integrate natively with Kingdee and Yonyou, the APAC subsidiaries will fight back — either by carving out their own shadow TMS, or by pushing to replace the recommended vendor entirely.
We have shipped dozens of production deployments where NiuX TMS sits in the middle of a mixed SAP + Kingdee + Yonyou landscape: steel groups, FMCG brand owners, pharmaceutical distribution, paper and pulp, building materials. In every one of them, the integration engineering was more about reliability across three different auth models and three different idempotency semantics than about any one protocol being “hard.”
The integration anti-patterns we refuse to sell
Some patterns get pitched frequently in enterprise TMS RFPs. They sound plausible in the deck. They consistently fail in production. We say so to prospects in the first call, and we route them to a different tier or a different vendor if they insist.
- “We integrate via our multi-tenant cloud middleware.” Translation: your ERP-to-TMS traffic leaves your enterprise perimeter, traverses a vendor-controlled integration plane, and returns. InfoSec will reject this on any regulated workload. Finance will reject it when the vendor raises the middleware per-transaction fee. Compliance will reject it the day there is a breach notification somewhere in the vendor’s stack.
- “We only do webhooks — you build the receiver.” Reliability of enterprise integration is a first-class vendor problem, not a customer problem. Making the customer implement retries, idempotency, dead-letter queues, and reconciliation for every endpoint is a way to move the reliability discussion off the roadmap while keeping it in the SLA spreadsheet.
- “All integration via CSV batch — it’s simpler.” CSV batches are a legitimate pattern for the right endpoints. They are a disaster as a universal answer. A waybill dispatched at 17:45 on Friday should not hit SAP at 06:00 on Monday. Some endpoints need seconds-level latency. Pretending they don’t is how you produce month-end surprises.
- “Our consultant will write custom ABAP for you.” Custom ABAP that no one at the vendor owns, that lives in your SAP namespace, and that the original consultant has left the country for — this is one of the most expensive technical debts an enterprise can inherit. When it’s genuinely required, it needs to be in the TMS vendor’s codebase, not in an untracked Word document.
How we scope an integration project in the first two weeks
No vendor can credibly commit to an ERP integration scope on a sales call. What we do commit to, in the first two weeks of a signed engagement, is an artifact that tells the joint team exactly what is being built:
- The integration matrix. Every endpoint listed with the seven attributes above. Reviewed and signed by the customer’s SAP/Kingdee/Yonyou owner, the customer’s InfoSec lead, and our integration engineer.
- The security model. Where the TMS talks to the ERP: which network segment, which firewall rule, which credential, which audit destination. Reviewed by the customer’s network architecture team.
- Sandbox provisioning. Customer provides a QAS/dev tenant of the ERP. NiuInfo provides a dev namespace of NiuX TMS. Neither of those is discretionary.
- The first round trip. A real master-data sync of one object type (usually material master) executed end-to-end on the sandboxes, measured on day 10–14, with visible logs on both sides. Before this is green, no functional scope progresses.
- The go-live gate. Production cutover is tied to a reconciliation report — what we sent equals what arrived equals what was posted — not to “everything seems to work.”
Customers frequently compare this scoping artifact to their RFP responses from other vendors. The difference — and this is not a sales point, it is a practical observation — is that the other responses are almost always written as “capability statements” (“we support SAP IDoc”), while this one is written as “work statements” (“here are the 11 endpoints we will build and the reconciliation gates on each”).
Close
TMS–ERP integration isn’t the hardest part of a transportation management deployment. It isn’t even the most expensive part. But it is the part that causes deployments to fail after go-live, quietly, over the course of months — not because the integration code was wrong, but because no one had named the endpoints, the owners, the reconciliation paths, or the operational alerts.
If you are evaluating NiuX TMS and the ERP question is the live one in your evaluation committee, the practical next step is short: send us a one-page sketch of your ERP landscape — which products, which deployment, which subsidiaries, which volumes — and we will come back with a first pass of the integration matrix before the next call. That is an engineering conversation, not a sales conversation, and it is the single cleanest way we know to de-risk what the committee is actually worried about.
If any of the above reads like the vendor pattern you’ve been trying to avoid, start the conversation here. The earlier the integration surface is specified, the smaller the deal risk on both sides.